In this final week, we ended up choosing a text summarizer for our final project. We used a summarizer that uses sequence to sequence algorithm that uses bidirectional LSTM for its encoder, RNN and LSTM for the decoder using Bahdanau Attention. The project use TensorFlow, nltk, numpy, pandas, and langdetect for the library. The datasets fits just right, we trained and tested the model. We were pretty satisfied with the model.
Intelligent Systems Blog 5
We started to work on our final project. One library is not enough, so we experimented with a couple libraries that could be used for Natural Language Processing. TensorFlow has their own library for NLP, and there is a thing called TensorHub by TensorFlow. It is an open source library from google, and is mostly used as the embedding layer for NLP.
Intelligent Systems Blog 4
During this week, i was absent. Though, i learned about computer vision and the library used for it. We tried openCV for computer vision. My team worked with Ivan’s team for the computer vision task.
For our final project, we found a suitable datasets. It was on Kaggle with the name of all the news. It contains 143,000 articles from 15 news publisher. The datasets also has the label that we want, therefore we decided to use the dataset.
Link can be found below for the dataset.
Intelligent Systems Blog 3
In this week, we learned about Naive-Bayes classifier. We found out that it is one of the algorithm used for text classifier. We also followed the tutorial on medium on text classification with spacy, but the datasets used was too big. They tried using yelp reviews dataset and use only the spacy library to classify the text. We found out that it wasn’t suitable for our project. We started looking for datasets that we want to use for our final project
Intelligent Systems Blog 2
It was on week 6, we learned about Apriori. My team tried to work on the final project by testing out the code given on the previous article on medium. The first part show how spacy work on python and what it does. We tried summarizing a paragraph with spacy in accordance to the tutorial. It worked fine, but took quite some time to summarize the paragraph.
Intelligent Systems Blog 1
This week we learned about K-Means algorithm. Our team decided to create a text categorizer for the final project. We did some research and found out that doing that requires an understanding in Natural Language Processing. There are some blogs on medium written by one of the team working on Spacy, a python library for NLP.
https://medium.com/@ageitgey/natural-language-processing-is-fun-9a0bff37854e
The article is divided into 4 parts. It explained clearly what NLP is and how it works.
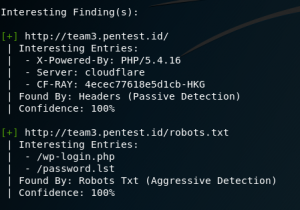
Using nikto to find vulnerabilities
Nikto
What is Nikto? Nikto is a server scanner that is able to scan potentially dangerous files, check outdated version of a software, and checking index files on a server. For more information about Nikto, you can find it on its official github right here
https://github.com/sullo/nikto
Steps:
- Open up kali linux machine
- Nikto is pre-installed on a kali linux OS based machine, to use it, type
nikto -h

- To run the scan, type the following command on your terminal
nikto -h target.host.ip.address
the target host ip address can also be changed to the website address

Using Google to find sensitive information
Google is a search engine that queries what the user search and find it throughout the whole internet. It can also be used by hackers to find sensitive information related to the target. The term that is used for google hacking is google dorks.
Steps:
- Open your browser and type google.com
- As cited on wikipedia, this are the most popular google dorks query on google.
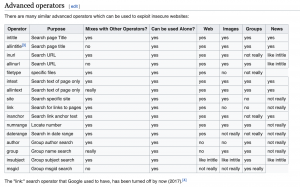
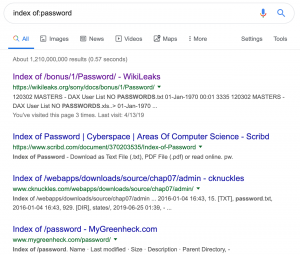
You can use this to find sensitive information, such as passwordlist, for example, by typingindex of:password
- You will find all related query on the result list
Brute Forcing WordPress website using wpscan
Steps:
- Open up kali linux terminal
- Type this command to brute force password on the wordpress admin login
wpscan –url TARGET.WEBSITE.COM -P PATH/TO/PASSWORD -U USERNAME
In this case, i put my wordlist on a file named password.lst and the username @user3
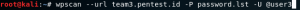
- It will run all the combinations of the username with all the word on password list
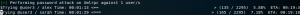
- If it matches, it will later notify the password
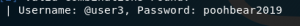
Using WPScan to find user on a WordPress based website
WPScan
What is wpscan? WPScan is a wordpress vulnerability scanner. It has many usage, among those the most useful are enumerating user, finding vulnerabilities, and brute forcing password on a wordpress site.
Steps:
- Open up Kali Linux terminal
- To enumerate user, use this command and press enter
wpscan --url WORDPRESS.WEBSITE.COM --enumerate u
In this case, i tried to find the user on team3.pentest.id
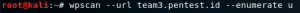
- It will then show the result of the finding.
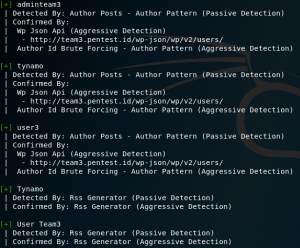
- It also shows some interesting finding on the website, such as its robot.txt content, server, étc.